Commercial Solutions for Classified Enables Mobile Command Posts
U.S. Army and Marine Corps tactical networking and command post programs have a widely acknowledged critical need to improve mobility, leading to the transition away from tent-based command posts to mobile, vehicle-mounted command posts that can move quickly.
The current state of the art for tent-based command posts requires hours of setup and thousands of feet of copper wiring that delay network availability, resulting in a dangerous lack of situational awareness for commanders.
To address this issue, the US Army recently launched a new program called Command Post Integrated Infrastructure (CPI2) to design and field vehicle-mounted command posts. One key technological goal of this program is “leveraging secure wireless technology for rapid connectivity”.
Secure Wireless Using Commercial Solutions
To enable mobility for warfighting, the National Security Agency (NSA) established a program (with a set of guidelines) called “Commercial Solutions for Classified” (CSfC). This program enables DoD organizations to transmit classified information using commercial-grade encryption solutions, eliminating the need for expensive, difficult-to-manage classified equipment. The ability of warfighters to securely transmit both classified and Controlled Unclassified Information (CUI) over Wi-Fi and LTE using smartphones, tablets, laptops and other Commercial Off-the-Shelf (COTS) mobile devices is a “need to have” capability for DoD warfighters. This is due to technology advancements made by adversaries that necessitate warfighters to have access to the same secure communications connectivity while on-the-move as they do at-the-halt. This further requires that communications solutions are delivered in a smaller form factor – whether to fit in a backpack of a dismounted soldier or integrated into a transport vehicle – and operate wirelessly.
CSfC enables access to classified information using inexpensive, commercial technologies, providing benefits such as:
• Enabling entirely new classes of wireless access to classified networks for warfighting
• Significantly reducing equipment costs and simplifying key management
• Simplifying equipment handling/security procedures
CSfC-based communications solutions transmit classified information via two layers of commercial encryption solutions. Previously, the only means to transmit classified information was via expensive, controlled, military grade encryption devices such as SECNET-54s and KG-250s.
The Figure 1 on next page demonstrates how classified information can be transmitted over non-secured wireless connections such as Wi-Fi, LTE, and SATCOM, including public, government and partner networks. This is achieved using two sets of encryption technologies, one layered inside the other. Approved configurations include encryption using VPN inside VPN, VPN inside Wi-Fi WPA2, MACsec inside VPN, and TLS inside VPN.
Organizations can select from a variety of technologies listed on the NSA CSfC Components List to create integrated solutions that enable classified networking over radio infrastructure such as SATCOM, Wi-Fi, LTE and mesh network, enabling vehicles to communicate with each other, to communicate with upper echelons/HQ, and enabling soldiers to use mobile devices such as laptops, tablets or smartphones, in transit, at the halt, and in dismounted use cases.
Mobile Command Post Communications using CSfC
The U.S. armed forces have called for more mobility, maneuverability, interoperability and reduced setup time for tactical command posts. To meet those objectives, command post programs are moving away from large complexes relying on multiple tents, to architectures based on vehicle-mounted communications shelters utilizing wireless technologies. This new approach promises to dramatically reduce setup time associated with constructing tents and data-center like infrastructure and laying thousands of feet of cable.
 A complete modern architecture for mobile command posts includes CSfC wireless, public key infrastructure, and cybersecurity infrastructure mounted on main command post platforms, and matching extension kits on remote (smaller) support vehicles. The main command post provides encryption, PKI and management services for the entire fleet of connected vehicles and end-user devices, and also provides Wi-Fi access points on the main command platforms for end-user Wi-Fi access.
A complete modern architecture for mobile command posts includes CSfC wireless, public key infrastructure, and cybersecurity infrastructure mounted on main command post platforms, and matching extension kits on remote (smaller) support vehicles. The main command post provides encryption, PKI and management services for the entire fleet of connected vehicles and end-user devices, and also provides Wi-Fi access points on the main command platforms for end-user Wi-Fi access.
On remote support vehicles and for Vehicle-to-Vehicle (V2V) communications, extension kits use CSfC layered IPsec VPN gateways over meshing radio, enabling the transport of one or more classified and/or unclassified networks between remote support vehicles and main command post vehicles.
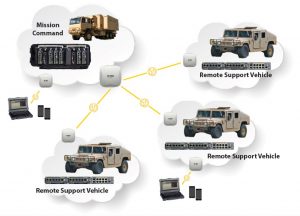 On remote support vehicles, for vehicle-to-end user (V2E) communications, the extension kits can include Wi-Fi access points configured to meet CSfC requirements that provide network access to end user devices such as laptops, tablets and smartphones. The remote Wi-Fi network can use layered encryption managed by the main command post vehicle, extending Wi-Fi services to remote vehicles while minimizing SWaP for those remote vehicles.
On remote support vehicles, for vehicle-to-end user (V2E) communications, the extension kits can include Wi-Fi access points configured to meet CSfC requirements that provide network access to end user devices such as laptops, tablets and smartphones. The remote Wi-Fi network can use layered encryption managed by the main command post vehicle, extending Wi-Fi services to remote vehicles while minimizing SWaP for those remote vehicles.
Size, Weight and Power
True mobility demands innovation and modernization designed to reduce size, weight, and power (SWaP) requirements. Not only do dismounted soldiers need mobility, but so does the network infrastructure to support them – when wireless infrastructure is vehicle-mounted.
To make this happen, programs are looking to small form factor, rugged, commercial-off-the-shelf technologies that fit within limited spaces and provide wireless network access inside vehicle shelters and between vehicles.
In contrast to legacy, data-center style 19” rack mount equipment, new generations of COTS equipment designed for tactical/expeditionary use are becoming available for use with CSfC-capable technologies. Additionally, with network function virtualization, many CSfC-required technologies may be co-located on a single server platform. Figure 3 on next page visually illustrates the size, weight and power savings with small form factor COTS equipment.
New tactical equipment, as compared to legacy 19” rack mount equipment, on average:
- Is 10.4 times lighter than a typical 1ru server
- Is 12.4 times smaller than a typical 1ru server
- Consumes up to 18 times less power
- These types of low SWaP solutions enable maximum program flexibility, enabling vehicle-mounted, roll-on/roll-off, fly away, and stationary use cases, all using the same hardware platform.
Ruggedization and Environmental Testing
To ensure reliable uptime of CSfC-based solutions in vehicle mount applications, components should be selected that have completed and passed a suite of MIL-STD testing appropriate for vehicle-mounted use cases, including environment, EMI and power (MIL-STD-810G, MIL-STD-461F and MIL-STD-704D). These tests must be conducted by independent, outside laboratories, and, where applicable, with the equipment powered on and operating.
Configuration Management and Monitoring
NSA CSfC requirements add complexity and training burden, imposed by the two layers of encryption and extensive security requirements. Organizations should consider CSfC-specific configuration management tools. These tools can simplify the setup, configuration, and management of the underlying equipment and devices used in CSfC solutions.
Such tools can provide a base level of capabilities which include:
- Enabling the deployment of CSfC solutions, with attendant benefits, while reducing the amount of added complexity and training
- Providing a unified interface (“a single pane of glass”) to underlying equipment from multiple vendors
- Providing means to monitor multiple sets of equipment, in fixed/branch offices and tactical settings, enabling lightly trained operators to manage the equipment
- Managing PKI, certificates, VPN and Wi-Fi encryption configuration to ensure compliance with security requirements.
 Available Now
Available Now
Available advancements in small form factor COTS hardware, virtualized networking and cybersecurity functions, combined with software management tools, make secure wireless mobile command posts possible – improving warfighter situational awareness, mobility and maneuverability – enabling US DoD overmatch and contributing to mission success.
Charlie Kawasaki, CISSP, is Chief Technical Officer at PacStar. Charlie joined PacStar in early 2005, and leads numerous innovation programs developing tactical solutions for secure wireless, cybersecurity and data center applications. Charlie is part of the PacStar team that recently won the networking equipment awards for both the US Army T2C2 and Marines NOTM vehicle-mount and deployable tactical communications programs. Charlie has over 35 years’ experience in cybersecurity, software and network engineering, and systems integration. He currently serves as a board member of the Technology Association of Oregon. He is vice-chair of the Oregon Cybersecurity Advisory Council (www.cyberoregon.com) , and is co-founder and manager of Northwest Cyber Camp (www.nwcyber.camp). For more information about new IT technologies transforming the battlefield visit www.pacstar.com.

